This is a guest post written by Elizabeth B. Vandesteeg, Financial Services and Restructuring Partner at Levenfeld Pearlstein, LLC.
Data breaches and privacy incidents have been on the rise in recent years, and information security is no longer something that companies can simply put on the backburner. Rather its imperative to effectively run your business and mitigate against substantial risk and cost. Information security refers to the processes and methodologies designed and implemented to protect print, electronic, or any other form of information or data including: confidential, private, and sensitive information; or data derived from unauthorized access, use, misuse, disclosure, destruction, modification, or disruption. An Information Security Program, or ISP, is a memorialized set of the company’s information security policies, guidelines, and procedures. The objective of an ISP is to assess risk, monitor threats, and mitigate cyber security attacks.
All companies, regardless of size should have an ISP. Whether or not your organization deals with a large quantity of personal identifiable information, your data could still be the target of an attack. Your own financial records, employee information, or other confidential information could be an attractive target for attackers as they could potentially sell or manipulate in other ways to make a profit.
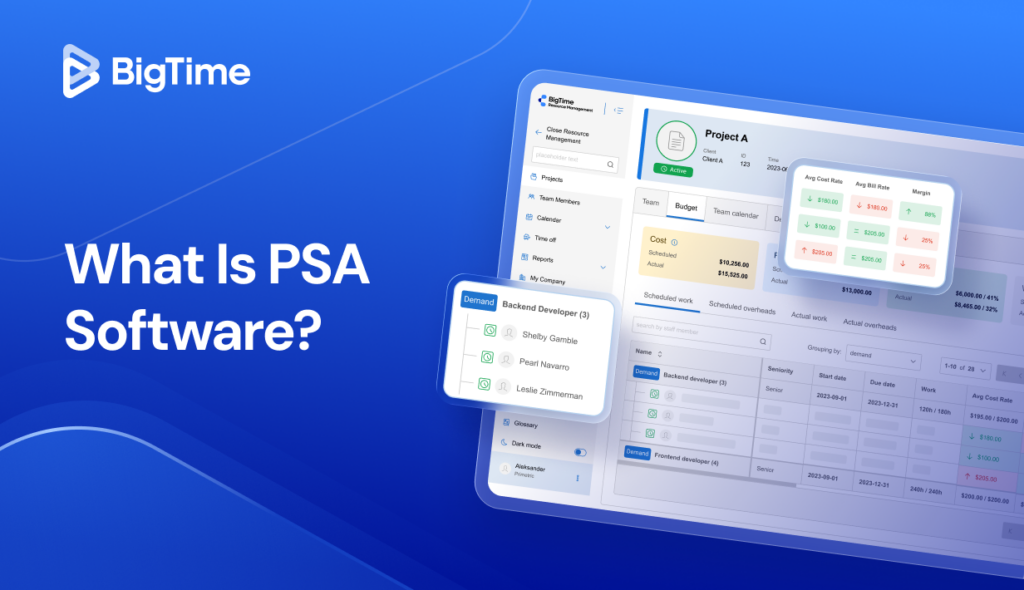
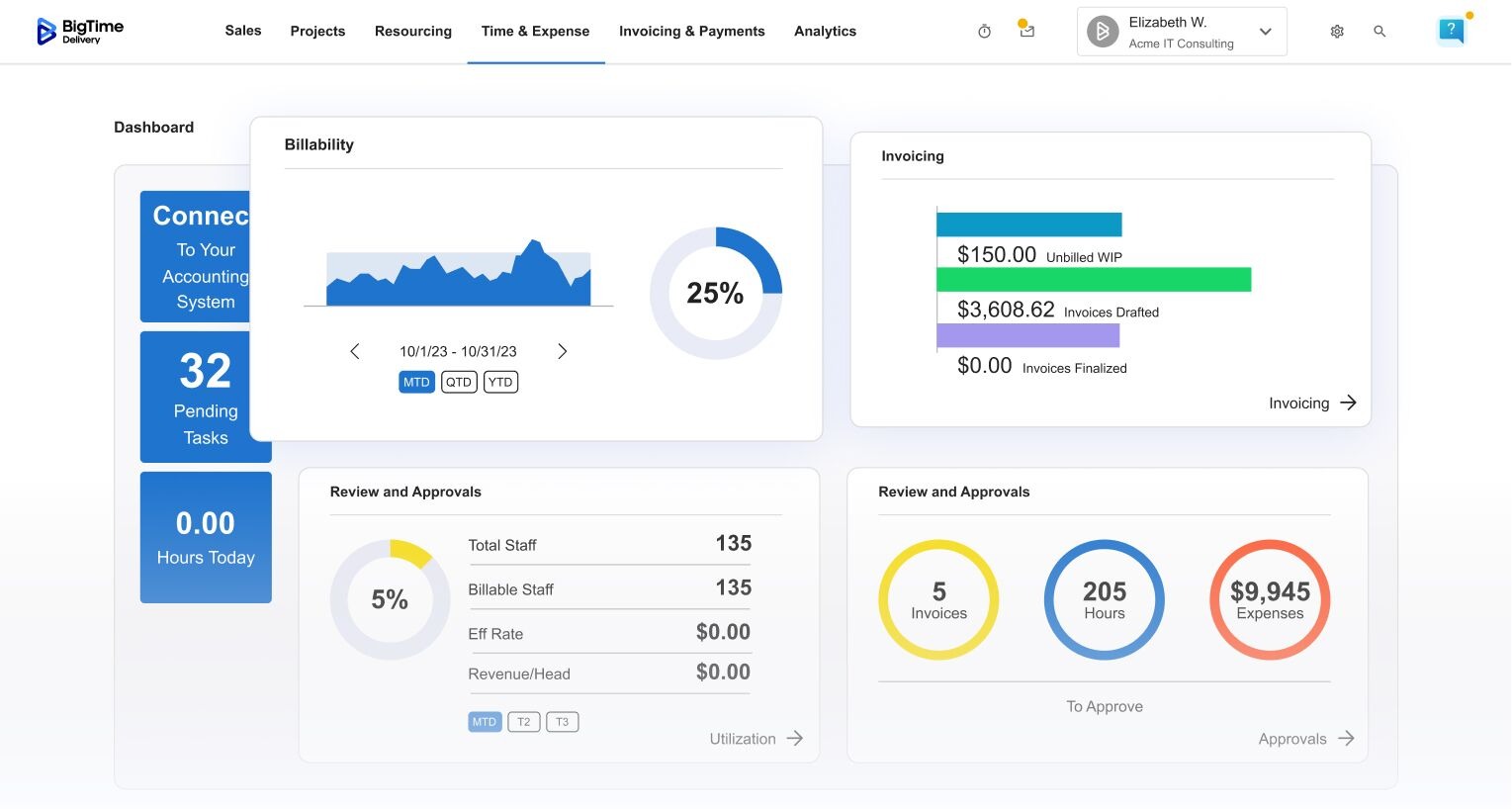
Learn what the CEO of BigTime has to say about the security benefits of cloud-based software in a recent 2022 predictions article.
Because an ISP is designed to mitigate the risk of an information security breach and meet compliance with regulatory requirements, a company’s ISP should focus on creating policies and procedures relating to the following: (1) data governance and classification; (2) access controls; (3) capacity and performance planning; (4) systems and network security; (5) systems and network monitoring; (6) systems and application development; (7) physical security and environmental controls; (8) risk assessment; (9) incident response; and (10) personnel training.
The following checklist is designed to help you create an ISP that meets the needs of your business:
- Does the ISP include a well-defined mission statement that includes the company’s main function, the role of the company’s security team, the company’s primary customers, the products and services that make up the revenue of your business, and the geographic location in which you operate (if relevant)?
- Does the ISP include the following elements?
- Purpose
- Scope
- Information security objectives
- Confidentiality, accessibility, and integrity of data
- Authority and access control policy
- Classification of data
- Data support and operations
- Security awareness sessions
- Responsibilities and duties of personnel
- Relevant laws (which may vary greatly depending on the states or countries in which your organization does business)
- Does the ISP anticipate and protect against the compromise of information security (i.e. misuse of data, networks, computer systems, and applications)?
- Does the ISP cover all data, programs, systems, facilities, personnel, and other technology infrastructure?
- Does the ISP implement the principle of least privilege?
- The principle of least privilege, an important concept of computer security, is the practice of limiting access rights for users, accounts, and computing processes to only those needed to do the job at hand.
- Privilege refers to the authorization to bypass certain security restraints. When applied to people, minimal privilege means enforcing the minimal level of user and access rights that still allow the user to perform their job function. When applied to processes, applications, systems, and devices, it refers to only having permissions required to perform authorized activities.
- Does the ISP differentiate between types of data and how each type is handled?
- Oftentimes, an ISP will classify data as high-risk, confidential, or public classes.
- High-risk data generally includes data protected by state and federal legislation; information covered under The Data Protection Act, HIPAA, and FERPA; financial information; payroll information; and personnel information.
- Confidential data may often include information that is not protected under law but should nonetheless be protected against unauthorized disclosure.
- Public data includes information that is freely distributed.
- Is there ISP security awareness within the organization?
- Companies should provide employees with training to help provide employees with information regarding how to collect/use/delete data maintain data quality, records management, confidentiality, privacy, appropriate utilization of IT systems, and correct usage of social networking, among other important data security measures.
- Does the ISP recognize the rights of customers (i.e. provide an effective mechanism for responding to complaints or requests)?
- Does the ISP identify an Incident Response Team to handle security incidents and data breaches?
Businesses should also obtain a cyber insurance policy as part of their overall security program. Insurance companies have recently become far stricter in underwriting these cyber policies. The implementation and evidence of a strong and thoughtful ISP can be a very effective tool for businesses to use in order to get better coverage for a lower premium.
The BigTime team obsesses over your company’s privacy and security. That’s why we encourage our clients to make the shift from accepting paper checks to adopting an integrated, online payment solution like BigTime Wallet. With online payments, this risk of identity theft and check fraud is significantly reduced. See what other security perks BigTime Wallet offers.